What Is Document Hashing? How It Prevents Tampering in Digital Signatures

Key Takeaways
- Document hashing creates a unique digital fingerprint, making any tampering instantly detectable.
- SHA-256 is the industry standard, approved by NIST and used in global regulations like ESIGN and eIDAS.
- Hashing is one-way and collision-resistant, meaning it cannot be reversed or easily duplicated.
- Digital signatures combine hashing with PKI to ensure authentication, integrity, and non-repudiation.
- Tamper detection is automatic, requiring no technical expertise from users.
- Document hashing supports legal compliance across standards like ESIGN, eIDAS, and HIPAA.
Document hashing in digital signatures is a cryptographic process that ensures a signed document cannot be altered without detection. It works by creating a unique digital fingerprint of a file, allowing systems to instantly verify whether any changes have been made after signing.
Have you ever wondered what happens after you sign a document electronically? How can you be certain that the contract you signed yesterday looks exactly the same today? What prevents someone from modifying key terms after you’ve already agreed?
These concerns are real. Document tampering can lead to financial loss, legal disputes, and compliance violations. That’s why modern electronic signature platforms rely on cryptographic hashing to guarantee document integrity.
Traditional paper signatures offer limited protection. Anyone with basic editing tools can scan a signed document, make changes, and print a new version. The signature may still appear valid, but the content underneath can be altered without detection.
This is where hash-based verification becomes essential.
Cryptographic hashing creates an invisible, tamper-evident seal around your electronic signatures. It functions like a unique digital DNA sequence that changes completely if even a single character in the document is modified. No special equipment is required, and verification happens automatically with mathematical certainty.
Here’s a simple way to understand it. Every time you sign a document digitally, the system generates a unique fingerprint for that exact version of the file. This fingerprint is extremely sensitive; changing a comma, adding a space, or modifying a single word produces an entirely different result. When the document is opened later, the system compares the current fingerprint with the original. If they don’t match exactly, tampering is immediately detected.

What Is Document Hashing in Digital Signatures?
Document hashing is a cryptographic process that converts any file into a fixed-length string of characters called a hash value or message digest. The concept is surprisingly straightforward.
Imagine taking a 50-page contract and running it through a special mathematical formula. This formula reads every single character, every space, every formatting detail. Then it produces a unique code that represents that exact document. This code is your hash value.
The process is completely one-way. You can create a hash from a document, but you cannot reverse the process. You cannot take a hash value and reconstruct the original document from it. This one-way nature makes hashing perfect for security purposes.
When you upload a contract for signing, a cryptographic hash function generates this fixed-length string from your document’s content. It should be hard to find two documents that hash to the same value. Given only a hash value, it should be practically impossible to figure out what the original document contained.
Different hashing algorithms exist. The most popular include SHA-256, SHA-3, and the older MD5. Among these options, SHA-256 has emerged as the gold standard for digital signatures because of its proven security track record.
How Document Hashing Works in Digital Signatures
The process involves several steps that work together to create an unbreakable security chain.
Step One: Document Upload When you upload a document, the system immediately generates a hash value using a cryptographic algorithm like SHA-256. This happens in milliseconds. The system reads every byte of your document and produces a unique 64-character string.
Step Two: Private Key Encryption. This hash value gets encrypted using the signer’s private key. This creates a signature that only you could have created. Your private key is secret. Only you possess it.
Step Three: Creating the Signature Package. The encrypted hash combines with your public key certificate and the original document. This package allows anyone to verify your signature without needing access to your private key.
Step Four: Verification When someone receives your signed document, the system generates a fresh hash from the current content. It then decrypts the original hash from your signature using your public key. If these two hash values match perfectly, the document hasn’t been altered.
This entire verification process happens automatically. Users simply see a “Verified” badge or a warning if something doesn’t match.

Why SHA-256 Is the Best Algorithm for Document Hashing
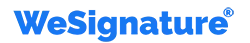
SHA-256 remains the most widely used and trusted hashing algorithm for digital signatures today. Different hashing algorithms exist. The most popular include SHA-256, SHA-3, and the older MD5.
Popular Hashing Algorithms Comparison
| Algorithm | Security Level | Collision Resistance | Recommended Use |
| MD5 | Low | Broken | Not recommended |
| SHA-1 | Medium | Vulnerable | Deprecated |
| SHA-256 | High | Very strong | Industry standard |
| SHA-3 | Very High | Extremely strong | Future-ready |
SHA-256 has emerged as the gold standard for digital signatures because of its proven security and widespread regulatory approval. SHA-256 stands for Secure Hash Algorithm 256-bit. The “256” refers to the length of the hash it produces. This length provides an astronomical number of possible combinations.
The algorithm enjoys widespread regulatory approval. SHA-256 is recommended or required by standards such as NIST SP 800-107 for digital signature algorithms and is compliant with eIDAS regulations in the EU for qualified electronic signatures.
SHA-256’s security strength lies in two critical properties: being one-way and collision-resistant.
The one-way property means SHA-256 is irrevocable. Once you create a hash from a document, you cannot work backward to reconstruct the original content. Even with unlimited computing power, reversing a SHA-256 hash remains mathematically impractical.
SHA-256 enhances electronic signature security through its collision-resistant properties, meaning it is computationally infeasible to find two different inputs producing the same hash. Even a single character change produces a completely different 64-character hash, making tampering immediately detectable.
The numbers are staggering. SHA-256 produces 2^256 possible hash values. Finding two documents with the same SHA-256 hash by chance is far less likely than randomly selecting the same atom twice from the entire universe.
This level of security explains why government agencies, financial institutions, and legal firms worldwide rely on SHA-256. The algorithm has been approved by the National Institute of Standards and Technology (NIST), the authoritative body on cryptographic standards.
How Document Hashing Prevents Tampering
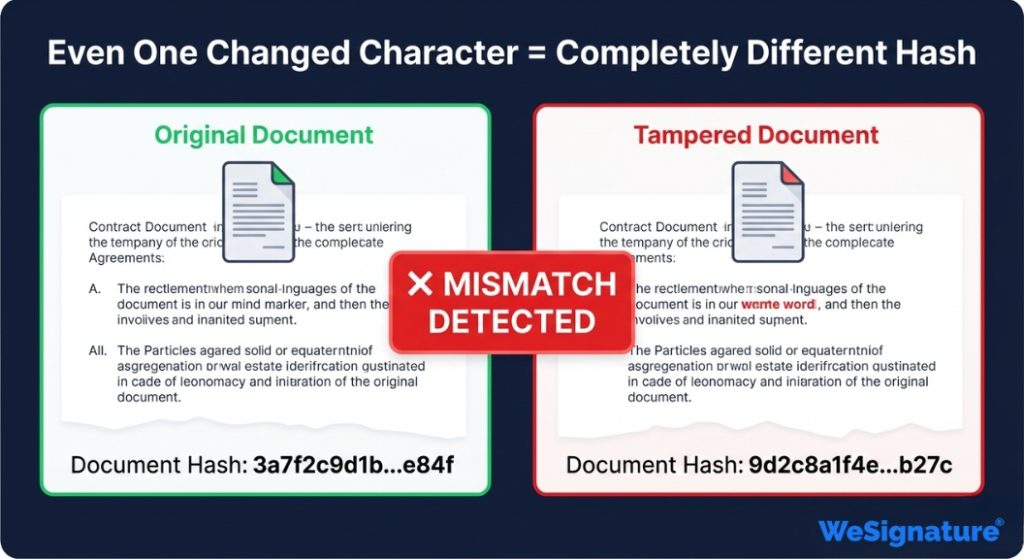
Every digitally signed document contains two critical pieces: the original hash value created during signing and the current document content.
When you need to verify a document’s integrity, the system generates a new hash from the current document. This fresh hash gets compared to the stored original hash from when the signature was applied.
If someone changes even a comma in your signed contract, the new hash will be completely different from the original. Not slightly different. Completely, utterly different. Every single one of those 64 characters will change.
This creates what cryptographers call an avalanche effect. A tiny change in input creates a massive change in output. The system doesn’t need to analyze what changed or where. The hash comparison tells you instantly whether the document is identical or has been altered.
Hashing during the creation of a digital signature allows us to provide authentication, non-repudiation, and integrity to a particular document. Authentication means you can verify who signed. Non-repudiation means the signer cannot deny signing. Integrity means you can verify nothing changed.
Modern platforms like WeSignature implement automatic tamper detection. The system monitors document integrity and immediately flags any discrepancies behind the scenes.
Legal Validity of Document Hashing in the United States
In the United States, document hashing in digital signatures is legally recognized under the ESIGN Act and the Uniform Electronic Transactions Act (UETA). These laws confirm that electronic signatures carry the same legal weight as handwritten signatures when proper security measures, such as cryptographic hashing, are used.
This means that documents secured with hashing algorithms such as SHA-256 are considered legally binding, provided the signing process includes identity verification, consent, and audit trails.
Businesses using compliant platforms like WeSignature automatically meet these requirements.
Real-World Uses of Document Hashing Across Industries
Legal Practice: Attorneys rely on hash-based signature blocks to ensure contract integrity. A single altered clause could change the entire meaning of an agreement. Hashing prevents such modifications from going unnoticed.
Healthcare: Healthcare organizations use document hashing to protect patient records and consent forms. HIPAA compliance requires strict document integrity controls. Hash-based verification provides the necessary security layer.
Financial Services: Financial institutions process thousands of loan agreements daily. Each document must remain unchanged from signing through the life of the loan. Document hashing provides this guarantee without slowing down operations.
Real Estate: Title companies use hash verification to ensure purchase agreements, disclosure forms, and closing documents remain pristine throughout the transaction process.
Document Hashing vs Encryption vs Digital Signatures
| Feature | Document Hashing | Encryption | Digital Signatures |
| Purpose | Ensure document integrity | Protect data confidentiality | Verify identity + integrity |
| Process Type | One-way (irreversible) | Two-way (reversible with key) | Combines hashing + encryption |
| Output | Fixed-length hash value | Encrypted data | Signed document with a certificate |
| Can it be reversed? | No | Yes (with key) | No |
| Detects tampering? | Yes | No | Yes |
| Used in e-signatures? | Core component | Supporting role | Primary mechanism |
| Example Algorithm | SHA-256 | AES-256 | RSA + SHA-256 |
This table highlights how document hashing differs from encryption and how both contribute to secure digital signatures.
How PKI and Audit Trails Secure Digital Signatures and Document Hashing
Document hashing works alongside Public Key Infrastructure (PKI) to create secure and verifiable digital signatures.
PKI uses a pair of cryptographic keys: a private key and a public key. The private key is kept secret by the signer, while the public key is shared with others. When a document is signed, the system generates a hash of the document and encrypts it using the signer’s private key. This encrypted hash becomes the digital signature.
Anyone receiving the document can decrypt the signature using the public key and compare it with a newly generated hash of the document. If both match, it confirms the document has not been altered and verifies the signer’s identity.
In addition to PKI, modern e-signature platforms maintain tamper-proof audit trails. These records include timestamps, document hashes, signer identity, and activity logs such as IP addresses and device details.
All audit data is securely hashed and stored, creating an immutable record of every action taken on the document. This ensures transparency, prevents tampering, and provides strong legal evidence in case of disputes.
Platforms like WeSignature manage this entire process automatically, allowing users to benefit from advanced cryptographic security without needing technical expertise.
When you use WeSignature for legal documents, the platform manages this complex PKI infrastructure automatically.
How WeSignature Uses Document Hashing to Secure Signatures
WeSignature protects every signature with enterprise-grade cryptographic hashing.
The moment you upload a document, the system generates a SHA-256 hash automatically. When you or recipients add signatures, the system creates new hashes that include the signature data. Each action creates a new layer in the hash chain.
Before finalizing, WeSignature verifies that the current document matches the original hash. This prevents document substitution during the signing process.
After signing completes, you receive a certificate of completion that includes all hash values. Anyone can use this certificate to verify the document’s authenticity independently.
This implementation follows NIST cryptographic standards and eIDAS requirements, ensuring global legal validity.
Common Misconceptions About Document Hashing
Myth: Hashing Encrypts Your Document Reality: Hashing creates a fingerprint. It doesn’t encrypt content. Your document remains readable.
Myth: All Hash Algorithms Are Equally Secure Reality: Older algorithms like MD5 have known vulnerabilities. Modern platforms should only use SHA-256 or SHA-3.
Myth: Hashing Slows Down Signing Reality: Modern hash functions work almost instantaneously. You won’t notice any delay.
Myth: Hash Verification Requires Technical Expertise Reality: Platforms like WeSignature handle verification automatically. Users just see a simple “verified” indicator.
Myth: Digital Signatures Can Be Easily Faked Reality: With proper hashing and PKI, forging a digital signature is mathematically impossible with current technology.
Final Thoughts
Document hashing in digital signatures is one of the most important advancements in modern contract security. It transforms electronic signatures into cryptographically verifiable proof, ensuring documents remain unchanged after signing.
Today, document hashing protects billions of transactions from legal agreements and financial contracts to healthcare records. While most users never see the underlying technology, it plays a critical role in maintaining trust, security, and compliance.
The strength of document hashing lies in its simplicity for users and its mathematical certainty behind the scenes. Once a document is signed, even the smallest change becomes immediately detectable through hash verification.
Platforms like WeSignature use secure hashing algorithms such as SHA-256 to provide tamper-evident digital signatures without adding complexity. This ensures every signed document remains valid, verifiable, and compliant with global standards. Whether you’re signing a simple agreement or a high-value contract, document hashing in digital signatures guarantees long-term integrity. The document you sign today can be verified years later with complete confidence.
As digital transactions continue to grow, secure hashing is no longer optional; it’s essential for preventing fraud and ensuring legal validity.
Ready to secure your documents? Start your free WeSignature trial today and experience tamper-proof digital signatures powered by document hashing.
Frequently Asked Questions
What is document hashing in digital signatures?
Document hashing in digital signatures is a cryptographic process that converts a document into a fixed-length code (hash). This hash acts as a digital fingerprint that changes if the document is modified, making tampering detectable.
How does SHA-256 prevent document tampering?
SHA-256 generates a unique 256-bit hash for each document. Any change, even a single character, produces a completely different hash, allowing systems to detect tampering instantly.
Are digital signatures with hashing legally binding?
Yes. Digital signatures that use secure hashing comply with laws like the ESIGN Act (US) and eIDAS (EU), making them legally equivalent to handwritten signatures.
What’s the difference between hashing and encryption?
Hashing is a one-way process used to verify data integrity. Encryption is a two-way process used to protect data confidentiality and can be reversed with a key.
Can a hash be reversed or reveal document contents?
No. Hash functions are one-way, meaning the original document cannot be reconstructed or revealed from its hash.
What is a hash collision, and is it a risk?
A hash collision occurs when two different inputs produce the same hash. With SHA-256, collisions are extremely unlikely due to the vast number of possible hash values.